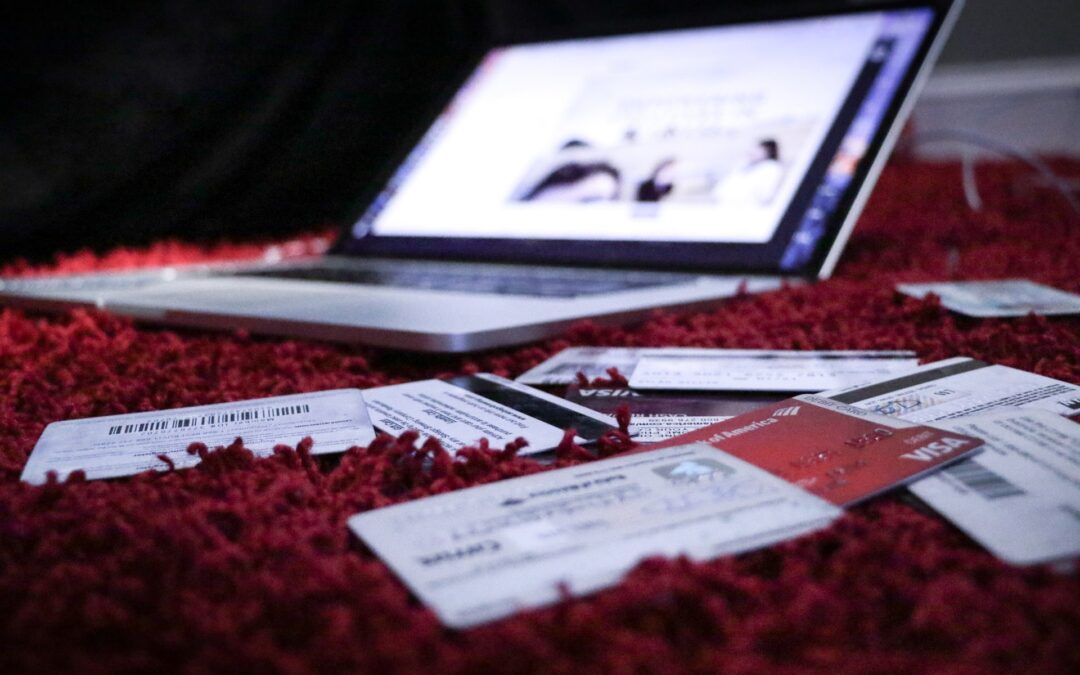
There’s a new type of credit card fraud that seems minor on the surface but is growing into a major issue. It’s called card testing fraud and it could affect you – big time.
What is Card Testing Fraud?
Card testing fraud occurs when someone comes into possession of stolen credit card numbers and they try to make small purchases online using those numbers. What they’re really doing is testing to see which of the stolen cards are still valid. If the purchases – typically the lowest-priced item or donation amount on your website – goes through, they know the card is still good and they can use it for further fraud. If the purchase is declined, the fraudsters know the card has been deactivated or is no longer valid, and thus of no use to them.
If a criminal decides to use your website for card testing you’re likely to see dozens if not hundreds of these attempted small transactions, all in a row. If a transaction is declined, you’re not out anything. If the transaction is approved, however, it’s likely the real owner of that credit card will eventually discover the fraudulent transaction, contact their credit card company, and dispute or reverse the transaction. This results in a chargeback to you, with all those associated costs.
How Does Card Testing Work?
There are two ways that criminals come into possession of credit card numbers. The first is totally random; that is, they use a computer-generated list of card numbers. The second method, which is much more common, involves purchasing batches of stolen card numbers from the dark web.
When criminals purchase large batches of stolen card numbers, they know that many will have since been deactivated but some will still be active and usable for further criminal activity. They need to test each number in the batch to see whether it’s still good or not, which is where card testing fraud comes in.
Some card testing is an attempt to fill in missing information for stolen card numbers. The thieves may have a card number but no expiration date. In this instance, they may try to run the same card number multiple times but with different expiration dates.
Most card testing is done automatically, via computer scripts or botnets of hijacked computers that can run thousands of transactions at a time. The script accesses a website, identifies the lowest-priced item or, on a church or non-profit site, the lowest donation amount, and then tries to initiate a transaction. The transaction is then either okayed (if the card is still valid and all the information is correct) or denied (if the card has expired or been deactivated, or doesn’t have the right address or expiration date).
The nature of how card numbers are obtained – stolen through large data breaches then sold illegally over the dark web – means that a majority of these stolen numbers are older and no longer valid. Some may have been used in fraud attempts in the past. Some, however, are fresher or have not previously been used, so the transactions will be approved.
As a church or non-profit organization, your problems start when the card owners notice the unauthorized transactions. For people who check their credit card accounts regularly, that may be the next day. For many people, however, they won’t see that transaction until they receive their credit card bill, which could be a month later. Some people, unfortunately, will never notice this first fraudulent transaction – but will see any further big purchases made by the fraudsters.
Is Your Church or Organization at Risk?
Any merchant, church, or non-profit organization that accepts credit cards online can be a victim of card testing fraud. In practice, however, these fraudsters tend to target small and medium-sized businesses that do not have the same security measures in place as larger retailers. They’re also particularly fond of church and non-profit websites for the same reasons, and because these sites deliberately make it easy for people to make legitimate donations.
Unfortunately, churches and non-profits can least afford the fees that accrue from mass card testing fraud. Many churches and organizations log on one morning to find their accounts socked with literally thousands of dollars of unexpected fees.
How Can You Spot Card Testing Fraud?
Card testing typically consists of multiple small dollar transactions from different card numbers submitted within a short period of time. Sometimes you may see multiple transactions from the same card number, but with different expiration dates each time.
You’ll know your site has been used for card testing when you see a large number of these small transactions either approved or declined. Expect to see a similarly large number of chargebacks show up in your account within a few days.
What Does Card Testing Fraud Cost You?
There are many detrimental effects of card testing fraud.
Naturally, card holders whose cards are still active will see the initial card testing fraud as just the beginning of long and financially painful experience. A criminal who finds a card number that tests okay will then use that card to make multiple subsequent purchases – typically within minutes or hours of the initial test.
For churches and non-profits, the costs of card testing fraud are many and substantial.
The biggest total cost typically comes from paying transaction fees for each of these multiple transaction attempts, whether approved or declined. With gateway and processing fees running $.20 to $.40 per transaction, having hundreds or thousands of fraudulent transactions run against your account can add up to big money fast.
Then there’s the cost that comes when a fraudulent transaction is initially approved but then disputed by the rightful card owner. You’ll receive a chargeback for that initial amount along with associated chargeback fees, which can often exceed the cost of that initial small purchase or donation. These chargeback fees can quickly add up when a fraudster bombards your site with a barrage of card testing attempts. The cost of these multiple fraud-related chargebacks have been so high that they’ve forced some businesses to shut their doors.
Even if your organization can afford to absorb these costs, the large number of chargebacks could exceed the thresholds set by your payment processor and risk placing you in expensive dispute monitoring programs. If the number of disputes is high enough you could lose access to payment processing completely.
Of course, you also have the expense of time and effort necessary to deal with all these chargebacks from the fraudulent activity. In addition to handling the paperwork associated with the chargebacks, some affected donors will contact you directly about these charges, and you’ll have to handle them, personally.
In other words, dealing with card testing fraud costs you both time and money.
How Can You Defend Against Card Testing Fraud?
There are several steps you can take to defend your church or non-profit against card testing fraud. Many of these security measures are simple to implement but have a big impact on the problem. Here are ten of the most effective things you can do.
1. Add a Captcha
One of the easiest ways to guard against automated transactions on your website is to add a captcha to your checkout, before a transaction is finalized. Captchas do a surprisingly effective job of stopping most scripts and bots, which are often used by card testers.
Most shopping carts have a captcha option. Your web developer should also be able to add a captcha to your site. The most popular and easiest-to-use captcha out there is Google’s reCAPTCHA, which is both effective and free.
2. Require CVV Numbers
Another effective approach is to set your CVV restrictions to block transactions with a missing or incorrect CVV number. Most card testers don’t have valid CVV data, so this will block their validation attempts – and, most likely, cause them to move on to a site that doesn’t employ this precaution.
3. Check Addresses and ZIP codes
Proper addresses and ZIP codes are unlikely to be attached to stolen credit card numbers, so card scammers often enter a random address and ZIP code when trying to complete a fraudulent transaction. Your payment processor can enable Address Verification Service (AVS) checking to make sure the address entered for the transaction matches that of the card used. IP geolocation checking can also be used to ensure the billing address provided matches the location of the IP address from where the transaction originates. If addresses or ZIP codes don’t match, it could be a fraudulent transaction. (It could also be that it’s a legitimate donor who’s traveling, so this method can return some false negatives.)
4. Block Multiple Transactions from the Same IP Address
Most scripts and bots try to conduct multiple transactions from the same IP address. You can set threshold limits so you can block more than a set number of purchases from a single IP address, and thus catch the majority of card testing attempts.
5. Limit Checkout Attempts
It isn’t just about multiple transactions from a single user. You should also limit the number of times that a buyer can attempt to complete an order in a single shopping cart session. This prevents card testers from using brute force attempts to enter acceptable addresses, ZIP codes, and the like.
6. Block Transactions from Outside the U.S.
It’s unfortunate, but most fraudulent card testers are located outside the United States, often in eastern Europe or Russia. Most shopping carts and payment gateways let you set IP restrictions to block transactions originating outside the U.S.
7. Require Donor Sign Up
Another way to discourage card testing is to eliminate guest checkout and require all transactions to come from registered donors. Requiring new users to go through a registration process will stop a majority of card testers.
8. Set Up a Firewall to Guard Against Botnets
Some prevention methods utilize technology. You should have a firewall already on your site; if not, install one. Most firewalls come with some sort of botnet prevention tools; if so, configure the firewall to detect and prevent access from botnets.
9. Use a Third-Party Fraud Monitoring Tool
Many third-party companies offer fraud monitoring tools designed to identify and protect against card testing and other fraudulent activity. Most of these tools let you enact the defensive options previously discussed, as well as guard against and alert you when fraudulent activity is detected.
10. Review Transactions Daily
Whatever other fraud prevention methods you employ, you should also review all your credit card transactions daily. This enables you to detect unusual activity and take action to block it.
Fraud-Blocking Options for PayTrace Customers
If your church or non-profit uses the PayTrace payment gateway through Higher Standards, there are several features available that can help block card testing fraud. These include:
- Duplicate Transaction Time, to prevent multiple transactions in set time period from the same card number
- Phishing Filter, to notify you and disable the card if there are more than three unsuccessful transactions from the same card number
- Require Billing Address, which disallows transactions without a billing address
- Require Billing ZIP Code, which disallows transactions without a ZIP code
- Require CSC, which disallows transactions without a CVV2/CSC code
- Address Verification System (AVS) Auto Void, which automatically voids transactions if the transaction response from the cardholder’s bank doesn’t match the billing address and/or ZIP code
- CSC Auto Void, which automatically voids transactions if the transaction response from the cardholder’s bank doesn’t match the CSC/CVV2 code on the card
- Manage IP Rules, which lets you restrict access to specific IP addresses
The Bottom Line
Card testing fraud is real and it could affect your organization. Contact your Give Back Gateway expert advisor to learn more about protecting your organization from this costly threat.

Recent Comments